SECURE NETWORK CLOUD ECOSYSTEM
Navigating Your Journey When There's No Destination
Security of the Network Cloud ecosystem is full of dynamic complications (i.e. it changes every day). The forces at play with vendors, service providers and cloud providers are all staking a claim for the biggest tech market of all time. Concepts such as “SASE” are center stage but the definitions are extremely subjective. At the end of the food chain are users: enterprises, organizations huge and small. This article examines the dynamics at play. The intention is to give the reader some insight and useful background on which to base decisions. Enjoy!
The following is based on the article published in the March/April 2023 edition of ISE magazine. Some minor additions reflect changes in perspectives on SASE/SSE and Zero Trust in the weeks following its completion.
People frequently talk about goals and objectives but for this author, it’s the journey experienced day-to-day that’s of more interest.
Especially as most thoughts about the future are based on a predictable past. This has never been more appropriate than when dealing with the network ecosystem.
This article is a review of today’s complex, seemingly chaotic network landscape. If nothing else, it’s important to be at ease with living with business and technologies in a state of constant migration— because that’s exactly where we are. The intention is to provide guidance on your journey. To begin, it’s important to start by looking at today’s reality about our Network Cloud Ecosystem.
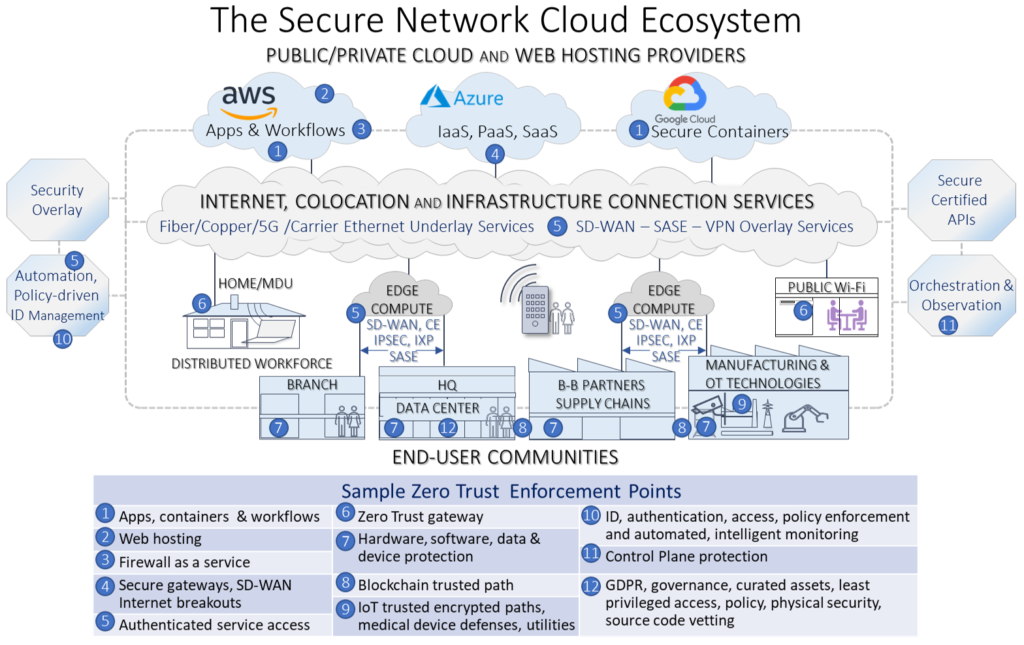
In my recent ISE Magazine article on holistic cybersecurity, we looked at Zero Trust being the only viable solution for the perimeter-less network.
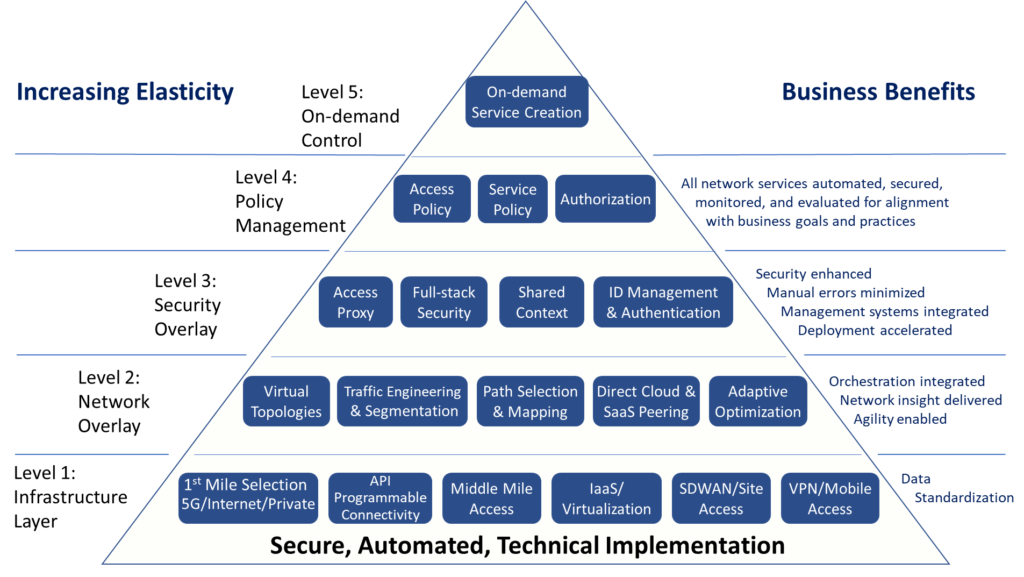
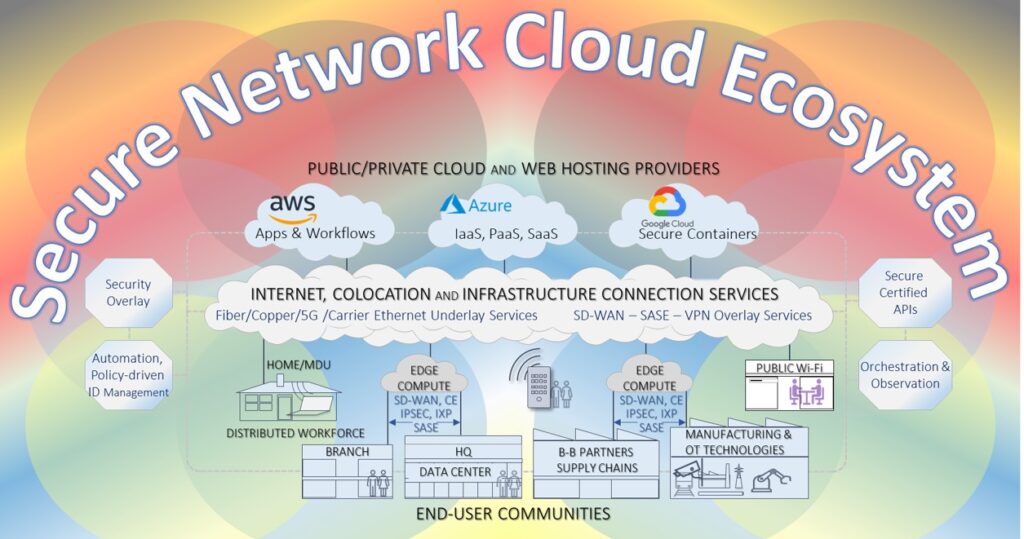
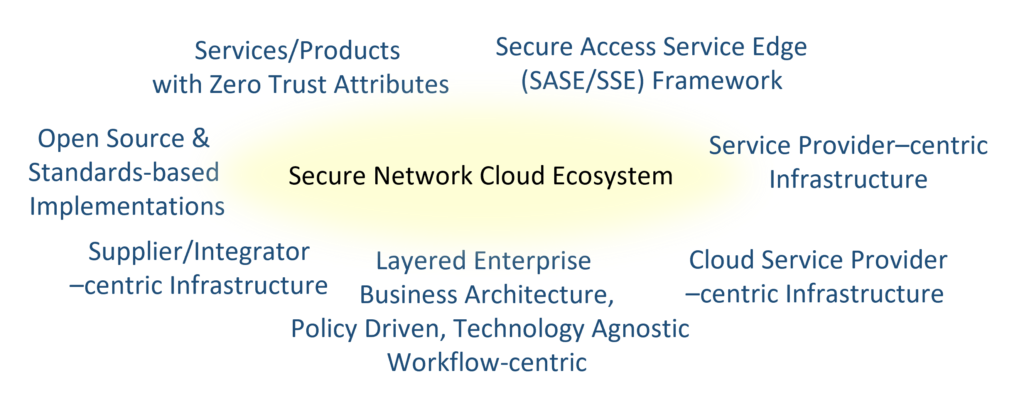
We called out the many potential enforcement points as we laid out the principal elements of the ecosystem as the backdrop in the chart below. It also called out the dynamics behind its evolution.
Despite the complex and evolving nature of our network environment, there are several other factors in play that are important to understand. These may not be obvious and are either overhyped or not spoken of at all. These are:
- Secure Access Service Edge and Secure Service Edge
- Standards and Open-Source Challenges
- Newly Available Standards
- Layered Business Architecture
- Service and Cloud Provider, Integrator and End-user perspectives.
People frequently talk about goals and objectives but for this author, it’s the journey experienced day-to-day that is of more interest.
Especially as most thoughts about the future are based on a predictable past. This has never been more appropriate than when dealing with the network ecosystem.
This article is a review of today’s complex, seemingly chaotic network landscape. If nothing else, it’s important to be at ease with living with business and technologies in a state of constant migration— because that’s exactly where we are. The intention is to provide guidance on your journey. To begin, it’s important to start by looking at today’s reality about our Network Cloud Ecosystem.
In my recent ISE Magazine article on holistic cybersecurity, we looked at Zero Trust being the only viable solution for the perimeter-less network.
We called out the many potential enforcement points as we laid out the principal elements of the ecosystem as the backdrop in the chart below. It also called out the dynamics behind its evolution.
Despite the complex and evolving nature of our network environment, there are several other factors in play that are important to understand. These may not be obvious and are either overhyped or not spoken of at all. These are:
- Secure Access Service Edge and Secure Service Edge
- Standards and Open-Source Challenges
- Newly Available Standards
- Layered Business Architecture
- Service and Cloud Provider, Integrator and End-user perspectives.
Since December 2019, when Gartner’s SASE blog envisaged a set of technologies, the network community was given a direction—the possibility of the secure integrated network ecosystem. One of the intentions was to bring networking and security companies solutions to work in harmony. A great idea that has created masses of hype and multibillion dollar analyst predictions. Soon after COVID-19 hit and Zero Trust became a necessity, SASE became even more important. Both were equally misinterpreted (I think I’m being polite). As we said at the beginning, it’s a journey that needs a 2023 reality check.
For those living under a rock for the last three years, with Secure Access Service Edge (SASE), Gartner called out (but did not define) SD-WAN “Overlay” services and network services “such as” Secure Web Gateway (SWG), Zero Trust Network Access (ZTNA), Firewall as a Service (FWaaS) and Cloud Access Security Broker (CASB), terming it all as SASE.
Essentially, SASE is a package of technologies including the core abilities above with the ability to identify sensitive data or malware and the ability to decrypt content at line speed, with continuous monitoring of sessions for risk and trust levels.
Today and tomorrow, that possibility is becoming a reality with around 50 suppliers, integrators, and service providers taking the journey to SASE, with a small number addressing all areas put forward by Gartner but a large number adding adjacent functions to combat a wider range of threats. However, any claims of compliance to the SASE model should be viewed with caution because frankly it’s a combination of services, not a definition of a standardized, cohesive, implementable framework. As you read the product reviews of solutions marketed as SASE, you should view them as earnest attempts at implementations that will, or may, eventually encompass all the important elements but for now represent some of the required components. Implementations themselves often blur the distinctions between the categories, none of which actually have an agreed standard definition, being proprietary in nature!
Even the recent NIST “Guide to a Secure Network Landscape should be read with this in mind covering ZTNA in only the vaguest of terms.
But wait, there’s more. Not only are there no standardized definitions but newer ideas have legitimately been rolled into one offering, for example, CASB and RBI (Remote Browser Isolation). RBI is a cool function, separating users’ devices from the act of Internet browsing by hosting and running all browsing sessions on a remote cloud-based, and hopefully secure, container. It helps prevent malware from being inadvertently loaded onto end user systems.
It also means that data can be screened to avoid exfiltration of sensitive data or access to middle box functions and as a phishing defense. It’s also an efficient way and place to implement a Zero Trust End Point. Perhaps daunted by the monster they had created, Gartner later created a milestone in the SASE roadmap termed Secure Service Edge (SSE) consisting of just SWG, CASB and ZTNA. Capabilities included access control, threat protection, data security, monitoring, and user control enforced by network and API-based integration. SSE is primarily delivered as a cloud-based service and may include on-prem or agent-based components. In March 2022, Gartner created a new magic quadrant summarizing 11 SSE players in this space.
It’s such a temptation for suppliers or service providers to wrap their products into “unique all-encompassing solutions” with the actual purpose of eliminating weak links being lost. I.e., the guidance of this article is to ignore any “complete SASE/SSE solution” hype and focus on matching what a product actually does against your current and anticipated business requirements.
We will discuss later a layered business architecture model that will handle migration and technology changes to help with such decisions. As I said upfront, this is a journey and it’s one worth taking. SASE and SSE are finding their way in the world.
So, where is all this headed?
As we said earlier, there are around 20 service products that claim to be SASE solutions, maybe 30 or so more that have SSE elements. There are another 30 threat prevention products designed to combat 30+ threat types. Some implement Zero Trust principles. It seems the best way forward is not to be swayed by either the buzzwords of SASE, SSE, the names or even the functions the product elements include but to focus on and understand the threats that products mitigate and see how they map to your requirements.
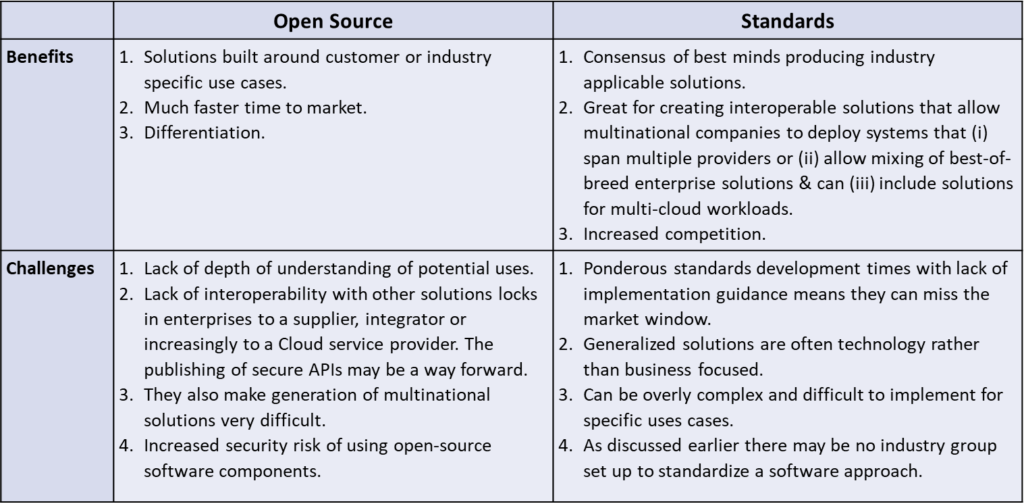
Standards and Open-Source Challenges
Having been on both sides of this discussion, it’s clear that both industry standards and open source have benefits and challenges. It’s also clear that if time to market is key then open source is the fastest but not often the cheapest approach. If multinational or multi-cloud approaches are critical, then standards-based approaches are advisable. Solutions that appear later based on standards can then be built in as a migration path.
In the next section, we look at some very recent standards that can be used to bring services and productsthat enable both SASE deployment and Zero Trust Enforcement to many points in the ecosystem including operational networks.
New Standards for the Secure Network Cloud Ecosystem
There are several standards related to implementing secure network ecosystem services. The SD-WAN service is well-established and two are new. The MEF (MEF.net) has produced standards for more than two decades and some recent ones are available to network equipment suppliers, security providers and service providers.
The latest iterations include MEF 70: SD-WAN Service Attributes and Framework published in 2021. This developing standard defines the externally visible behavior of an SD-WAN Service based as an agreement between an SD-WAN subscriber (buyer) and a service provider (seller) agreement on the values of a set of SD-WAN service attributes.
This is game changing. For instance, it could also be applied in Zero Trust-based services such as ZTNA, as part of the aforementioned SASE and also in areas of enterprise operational networks.
It handles interactions between subject and target actors that can be users, applications, or devices such as IoT devices in operational networks.
It enables standardization between applications and multi-cloud and computer edge workflows. The author of this article was privileged to be a contributor to this important standard over the last two years.
In November 2022, The MEF also published its SASE Service and Service Attributes definition MEF 117 by defining a standard combining security functions and network connectivity as an enabler of SASE services. It defines a service framework and specifies service attributes that need to be agreed between a service provider and a subscriber for SASE services, including security functions, policies, and connectivity services.
These specifications, in conjunction with proprietary SWG, CASB, FWaaS and RBI services, can be the basis of a network journey is never robust SASE offering and a far-reaching enterprise network solution.
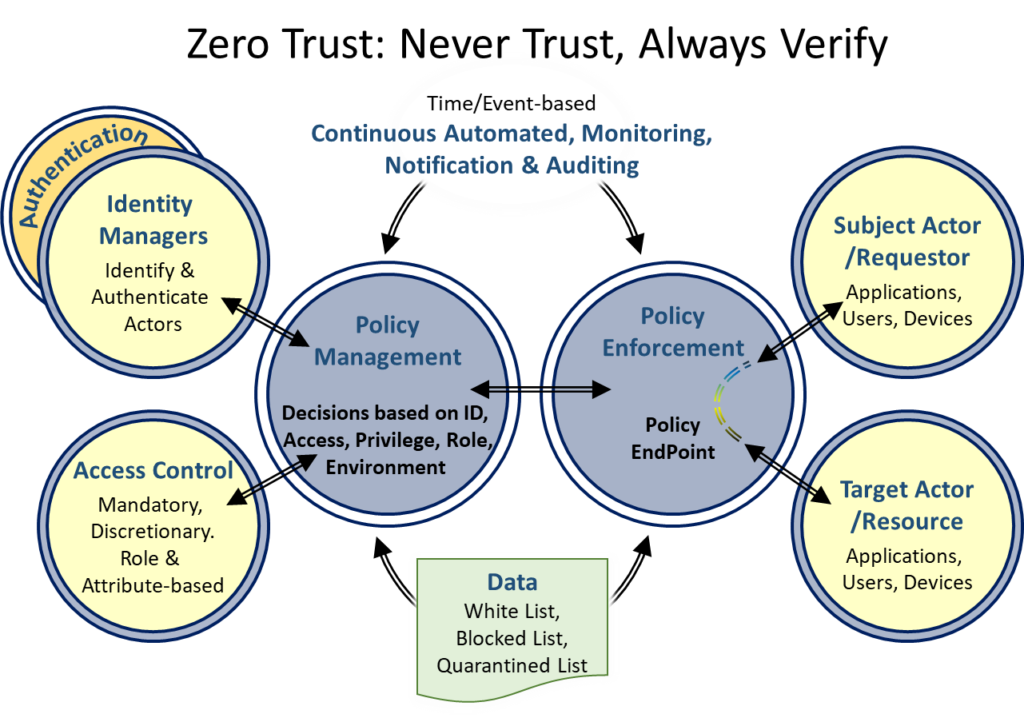
The MEF’s Zero Trust Service Attributes Framework (MEF 118) defines attributes that enable services to implement Zero Trust principles and strategies into a network service deployed anywhere in the network.
This standard handles user, application and device identity, authentication, access control based on roles and attributes, policy enforcement at policy endpoints and continuous monitoring as shown in the Figure on the right. Its initial intention covers many use cases of potential Zero Trust-based services.
A Layered Business Architecture
From an end-user’s organizational perspective, particularly larger enterprise and government bodies, the focus is on business agility, cost, scale and, of course, security. This is an important topic for the Open Networking Group (ONUG. net). ONUG represents the voice of the enterprise providing that community with guidance on the evolving network cloud. The Network Cloud Working group, of which this author is a member, recently published a layered business Network Cloud Playbook is driven by business policy as shown on the right and is intended to be capable of being able to replace network elements and infrastructure as dictated by changes in policies and on demand. It ties back to this article’s theme that the network journey is never complete but in a constant state of migration. Its intention is to empower enterprises and businesses in general to choose an infrastructure that supports their unique business requirements.
Service & Cloud Providers, Integrators, Suppliers and End-User Perspectives
The final piece of this article covers the market dynamics. This is important because it gives you the context of the sales and purchasing discussions. Everyone wants to be in control. If you are an Enterprise, then you will relate to the business-oriented Network Cloud Playbook. You may also like to visit my website (cybyr.com) covering the importance of taking a holistic approach to cybersecurity across your all departments in your organization, distributed workers, contractors and supply chains. I.e., SASE and Zero Trust are important but they only address a small part of the cybersecurity landscape.
Cybyr.com also breaks news of the latest threats and developments including explaining 150+ cybersecurity terms. From the perspective of service providers, cloud providers, integrators, equipment suppliers, software and security companies—everyone wants to be in control and will claim to have a complete solution and build a wall around you and your purchases.
There are many forces in play in the evolving, dynamic Secure Network Cloud Ecosystem, some business, some technical and many commercial as summarized in the figure on the left. For end-user organizations it comes down to budget, control, security, and your ability to contractually bind your suppliers to their performance and ability to deliver high performance, high security solutions no matter what they are called or branded.
As they say in Zero Trust, Don’t Trust, Verify. My hope is that my personal perspective gives a balanced view bringing some order to the incredibly fast-moving pace of network change. For the most part it’s important to enjoy the journey and be flexible as the path to the perfect network will likely keep taking new turns.

Mark Fishburn | Providing Strategic Marketing for Cybersecurity as a Service, Network Services. Publisher of the Holistic Cybersecurity book: Hey Who Left The Back Door Open? (on Amazon). Current participant in ONUG Network Cloud & Securiity Working Groups MEF cybersecurity and technical and test initiatitves. Learn more by visiting https://cybyr.com. Follow him on LinkedIn.