HARMONIZING HUMAN AND AI STRENGTHS
Intention
Today, most people are using AI every day. In last summer’s issue of ISE magazine, I covered the strengths and limitations of AI and humans. This initative takes these ideas to a new level, harmonizing the human and AI strengths into a new way of thinking and operating.
- Most human strengths are incorporated in the Transformative part of our Cybyr-AI expert-guided AI software.
- Cybyr-AI’s Informative sections includes an early implementation of a Managed AI Agent together with up-to-the moment cybersecurity and AI intellegence.
- The complete set of human strengths are delivered as part of our Virtual CSO Service.
- Above in May 2026, the main lesson to be learned is that AI and cybersecurity are both holistic spanning all aspects of the endeavors. What is clear is that we are all on this disrupting and exciting journey together with the outcome is intuited without being known.
The journey continues …
Impact
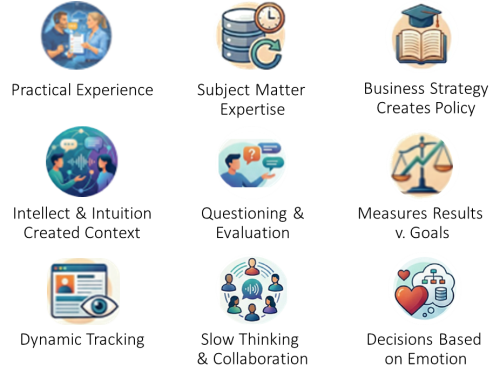
The focus continues to be on Small and Medium Businesses, who are driven by operating their businesses, not by these topics. There are one hundred million small and medium businesses that need help. The service provider readers of this initiative serving those SMBs have an important role to play too. Let’s begin by distinguishing nine human strengths. Large organizations are leading the way but the principles are the same.
The goal is to harmonize those human and AI strengths leading to an exponential increase in productivity, security and an upgraded working life.
What are the ten human strengths that AI does not have (yet!)?
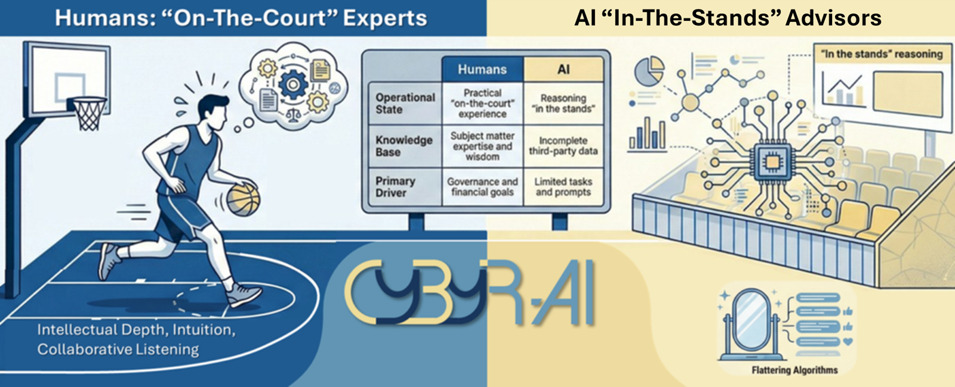
| Humans | AI | |
 | Have Practical “on-the-court” use cases—actual experience with constraints and accountability. | Has no practical experience, as it’s clever software reasoning from aggregated data “in the stands.” |
 | Have subject matter expertise, judgment and wisdom based on relevant context. | Only partially understands concepts, relying on user-supplied user context and vast quantities of incomplete third-party data. |
 | Actions are governed by strategies, policies perceived business and operational resiliency, creativity, governance and financial goals | Operates in limited dimensions based on specific tasks, limited by prompts. |
 | Bring intellectual/contextual depth, intuition and innovation for dynamic interaction and influence to anticipate trends. | Is passive: “Ready when you are.” “Ask me anything.” Conversely, it recently became capable of making unilateral unsupervised decisions that can be high risk. |
 | Are proactive, questioning users. Bring guidance and recommendations to users or collaborators based on responses and interactions. | Does not lead interactions. It does respond to prompts with extraordinary, filtered information to augment human understanding – all at lightning speed. |
 | Measure results over time, tracking progress in organizational strength and reduced risks. | Does not have the human wisdom to prioritize the importance of its data subjectively as it relates to individual use cases. |
 | Continually track news in real time, evaluating opinions, technical and business impact from many sources. | Is not connected to the moment-by-moment news. Often in a narrow and sometimes dated focus, especially in private LLMs. |
 | Listens slowly, playing new ideas against what they already know, often leveraging collaborative groups | Is an algorithm that uses non-attributed data, creating an error-prone, trial-and-error system. Unless constantly supervised, it drowns its human user with unrequested information. Although it draws on masses of information it only discusses it with one user. |
 | Make decisions based on many subjective criteria, drawing on the power of language to influence emotions, spoken, written and visual interactions. | Is programmed to deliver flattering communications to support algorithm-based opinions based on insecure information or from unverified sources. |

Leadership - we left the best till last!
Above all other strengths, humans can bring leadership qualities needed to inspire, empower and set transformative purpose for individuals, organizations and communities.
Applying AI to Resilience and Cybersecurity
Next is a list of the application of human and AI strengths, structured as critical organizational layers that dictate the business strength and security of the organization.
The approach of the Cybyr-AI and Cybyr.com’s Virtual CSO service software is to blend the various human strengths, cybersecurity expertise and AI/ML approaches, tempered with current thinking. The result is an inclusive and rich experience.

Executive Commitment and Accountability
Having resilience, security and AI as executive accountability is the only way to consistently manage and be responsible across the whole organization. Don’t do this, and you can forget the rest of this list. The use of language is so critical here to inspire and motivate the benefits.
Cybyr-AI Expert Proactive Interrogation.
Makes Recommendations based on experience to establish holistic framework and best practices. This establishes business-focused and accountability.
Cybyr.com Virtual CSO Service
Makes Recommendations to establish holistic framework and best practices, establishes business focus and accountability. Implements as required, introduces executive-level communications and resilience, competitive advantages and strengths. Intentioan is to leave the organization with executive level CRO, CSO, CAIO accountability.

Policy and Plans
Having a policy that includes a financial framework is the only way to create the context for a regular and measurable (say quarterly) plan. This creates a clear competitive advantage, not forgetting that good documentation can be the best defense against liability
Cybyr-AI Expert Proactive Interrogation.
Explores user policy and quarterly step-by-step plans. Makes recommendations, templates and customed policies and executing plans and reporting based on organizational strategy. A policy regarding the use of AI and its security guardrails also belongs as an executive responsibility
Cybyr.com Virtual CSO Service
Provides Security, Resilience and AI Policy and Planning templates and where required implementation and regular executive level reports of progress v. collaborative goals and governance.
Asset Stewardship
Asset Stewardship is about limiting exposure, protecting assets, and testing the Resilience Plan. Managing who, what, where, and how systems can be accessed is governed by policy. Micro-segmentation access policy and making data assets only visible to authorized software.
Cybyr-AI brings the latest expert guidance and establishes the foundation for strengthening the organizations competitive position, implementing well documented procedures as the fundamentals of defense. It addresses the verficiation of testing the resilience and security of implemented systems. This where the ability to lead organizations to new opportunities to enhance the competitiveness are integral to the recommendations.
Human & System Access, Interactions
Human & System Access & Interactions are about insider threat vetting, best practices for phishing prevention and policy for systems access. Indentity, privilege and social engineering are critical.
Cybyr-AI evaluates vulnerabilites across the entire organization. Its motto is “you are only as strong as your weakest link.”
VSCO service work includes investigation and motivation of staff beyond their normal experience. Of particular importance is the ability of TI to ensure all staff implement automated processes to avoid human error.

Supply Chain Management
Supply Chain Management requires knowledge of and verification of all manner of suppliers and third parties, with collaboration to avoid abdicating responsibility.
Cybyr-AI applies expert verification to avoid abdicating responsibilities. Cybyr-AI investigates the 68% of vulnerabilites that are beyond the scope of IT as well today’s IT realities.
VCSO Services provide a hands-on investigation especially when negotiating with suppliers of all kinds. This means outsourced everything from elevetor engineers, security cameras, badge readers to companies embedding open-source software in their products, those not implementing DevSecOps, understanding the security policy of CPAs, CRM and web hosting companies. These require deploying human strengths.

Human & System Access, Interactions
Holistic Organizational Integrity is an oversight of every department and their third-party contractors and suppliers to understand risks.
Cybr-AI investigates the organization’s oversight into recruiting, ascertaining potential social engineering and insider threats. It also manages the implementation of access to corporate systems, privilege levels acceptable locations for transactions etc. It laso looks acceptable location and device usage for staff, contractors and third parties. `

Basic Software Protection
Basic Software Protection. It still amazes me that most companies still use passwords and have no multifactor authentication. This is the first place that requires some low-cost outside spend.
Cybr-aI uses agentic AI based recommendations to ensure that current bast practices for basic security are implemented. This includes product selection.

Zero Trust
Zero Trust is the only recognized framework for real defense: identity management, authentication, policy and security management and enforcement being key. It is critical to apply zero trust for all user, software and device transactions. Applying the latest verification of all products security – especially security products aligned with the latest Mythos/MDASH approaches.
Cybyr-AI interrogates the use of Zero Trust Principals in use for the above work both internally and in the security attributes of contracted provider services. The latest twist on Zero Trust is the ability to provide autonomous AI agents as actors with the same level of Identity, not just for users, software and devices.

Assume Breach: Threat Detection and Removal
Despite everything, breaches will happen. The key is detecting and removing breaches instigated with AI or Ransomware as a Service before they cause damage or worse. Service providers are best placed to address this threat.
Cyber AI interactions lead to recommendations of when and where to use XDR (Extended Detection and Removal) software usually by service providers or Endpoint Detection and removal software. As indicated above, transactions are no longer between subject and target actors but now include autonomous AI agents tat must be properperly identifiied authentincated and authorized.

Monitor Everything: Verify Live Performance New Developments.
Everything must be monitored for ongoing improvement, constant evolution in threats and measurement of planned actions.
Use of Agentic AI is becoming mandatory for the monitoring and blocking many transaction types. Cybr-AI provides evaluation and recommendations. It also takes responsibility for measuring overall corporate organization strength and risk measurement over time against security plan goals.
Applying Human Strengths with Cybyr.com's Virtual Chief Security Officer Service.
As we said earlier, humans make decisions based on many subjective criteria, often based on the power of language to influence emotions, spoken, written and visual interactions. On the negative side they can get stuck in their past that overly influence decisions.
This is where Cyby.com’s VSCO service comes into play, bridging the worlds of technical considerations and business imperatives to ensure that conculsions and policy implementation are delivered in a language that resonates with executve conversations.
There is so much more to each aspect of Cybyr-AIs up-to-the moment informative content. We still hardly scratched the surface. This page is subject to continual update as the fast moving world of managed AI agents and initiatives influence cybersecurity.