ZERO TRUST
A set of principles and strategies to prevent and be resilient to cyber attacks
by eliminating trust and nullifying breaches that have already occurred.
Updated May 2026
Zero Trust has been defined by the National Security Telecommunications Advisory committee. This slightly tweaked version tidies up a couple of inconsistencies.
Zero Trust is a cybersecurity strategy premised on the idea that no asset (user, software, device) or transaction between them is to be trusted. It assumes that a breach has already occurred or will occur, and therefore access to information is only to be granted only while the transactions between assets are valid as compliant to the policy in place.
In 2026, John Kindervag, has been using this shorter definition:
Zero Trust is a strategy designed to stop data breaches and prevent other cyber-attacks from being successful by eliminating trust from digital systems.
The reason for many definitions is that as it evolves practioners are constantly refining and explaining their own understanding – to themselves! This is a healthy demonstration of the works journey.
It’s never a single or complete solution for IT, Networking,etc. – don’t be persuaded otherwise. You will have many context-dependent implementations across your organization and ecosystem. The defense deployed depends upon on the specific threat.
Only when you look at Cybersecurity holistically, does it become blindingly obvious that Zero Trust is a mind set, an organizational and technical strategy and why it should shape your organization’s thinking.
The Cause - why Zero Trust has become and will remain critical.

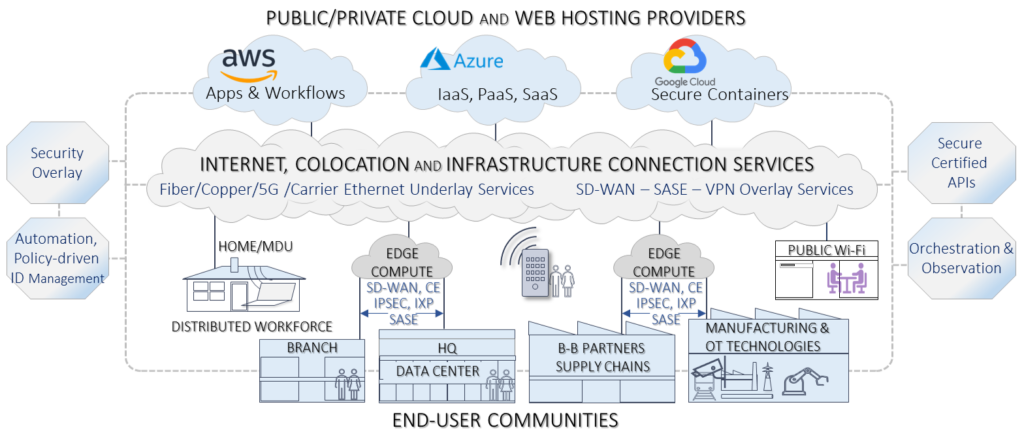
The Network Cloud Ecosystem (shown below), Network as a Service, distributed workforces, supply chain and open source software weaknesses means the network perimeter no longer exists to be defended.
Exploitation

State-sponsored threats change daily: from Phishing/Ransomware-as-a-Service, Advanced Persistent Attacks, Living-off-the-land attacks, lateral movement, insider and supply chain threats, etc. – and that’s just scratching the surface. They all prey on the vulnerabilities exposed by creation of the dynamic ecosystem shown above.
Why Now?
The cause and resulting exploitation above show why Zero Trust principles and strategies, when applied, have become so relevant. Although coined more than a decade ago, Zero Trust today represents the only viable defensive approach.
Principles and Strategies

Zero Trust Principles:
Never Trust, Always and constantly Verify | Assume Breach | Access using Least Privilege | Prevent exfiltration of data as opposed to just preventing access to data.


Zero Trust Strategies:
Begin with a top level Security Policy to decide what should be protected and curate those resources to create resilience to your critical assets.
Then understand your deployment of Identity management and authentication of actors – users, software, devices | authorize via actor-specific, attribute-based policies, controls, management and enforcement | automated, constant, time-sensitive monitoring to ensure ongoing verification and prevent trusted actors becoming threat actors | prevention, testing and remediation | automation is critical to ensure created assets are up-to-date and to elimate human errors.
Create Business Resilience by planning seamless recovery. Become a steward protecting data, software, devices and services. Have rigorous testing of backed-up assets become the norm.
Step-by-step, form an ongoing Zero Trust strategy for your journey, measure your progress. Rinse and repeat.
Holistic Cybersecurity and Zero Trust
Encompassing Organization and Technology
The best approach to eliminate hundreds of weak links is a holistic one that begins with the executive team, includes the whole organization and ensures proper delegation to external contractors and supply chains.
Zero Trust applies across the organization not just to Information Technology with only 32% of actions within IT. The remainder are distributed across the organization: Exec Team 15% Asset curation 14%, Operations 10%, HR 8%, etc. The management of a holistic approach requires AI and human strengths. See the Integration page for the nine human stengths and areas of the organation to be addressed
Implementation Journey - The 5 Step Methodology

Zero Trust Framework
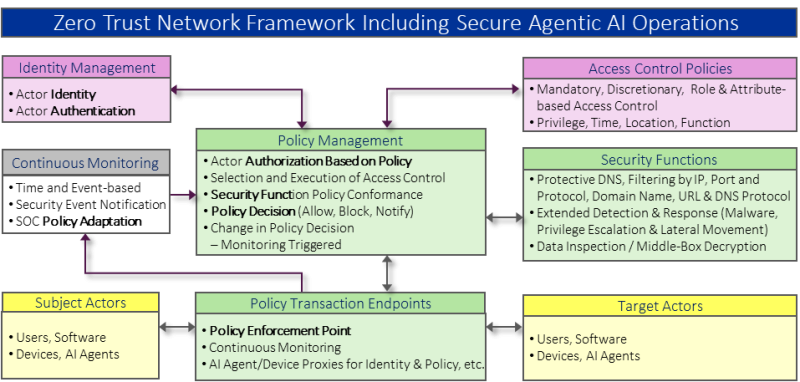
Our Cyberpedia page goes into detail on the terms used. However the term “Actor” is applied to any user, software (application, network systems or management) process, or device that initiates a transaction (Subject Actor) with a (Target) Actor.
Indentity of transient elements such as AI agents also fall into the application category. At time of writing the approach to Agentic AI has not been standardized. The Policy Management system is the authorizing process that allows or blocks transactions based on identity, authentication and policy. The decision to authorize is typically based on many security functions shown below. Details on security functions are covered in the Cyberpedia page.
This is a framework is a guide rather than a an implementation plan. However it is ideally implemented by a service provider who can best detect “Lateral Movement” attacks, being the trademark of ransomware attacks. See “Assume Breach.”
Deployment

Where Should Zero Trust Be Deployed?
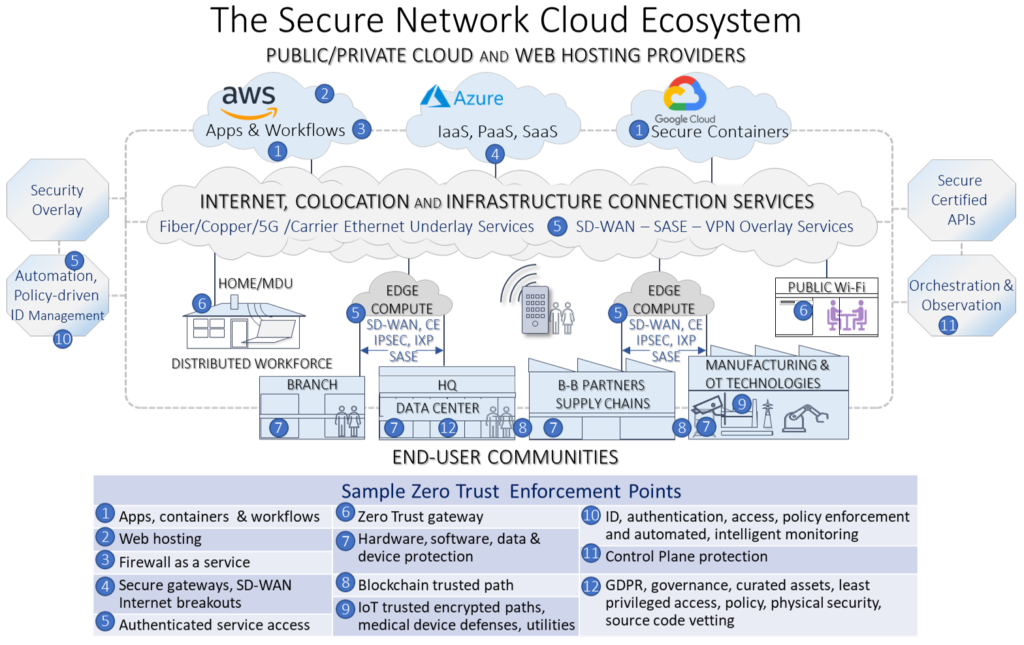
The chart below makes it obvious why there cannot be a single Zero Trust solution! Map the diagram onto your organization, download the top ten list from cybyr.com, then read the book, and decide what matches the assets you need to curate and protect.
Deployment of solutions that enforce and implement the strategies may span several locations over a Trusted Path or workflow, or at a single location and at various layers. the chart below shows the many “Policy Enforcement Points” indicated in the above framework.
Step-by-Step, starting with the most important areas to protect, map the access and flows to and through each point, plan the Zero Tust elements and monitoring. Bake this into your Security Strategy.
Zero Trust is a Journey
Finally, don’t be daunted. Zero Trust is not an overnight fix. It’s a constant journey that begins with asset curation to identify the most critical assets to protect first. Each action you take addresses your vulnerability, strengthens your weakest links and reduces your risks. Keep aware of new threats and developments such as those listed on the breaking news section of this site. Expand your understanding by reviewing the 430+ cybersecurity terms covered on this site. Use our Security as a Service software to measure your progress. If you are challenged with stress or burnout, then Zero Trust can help here too. It has hidden power!

