Cybyr-AI Help System
Table of contents

Overview These pages provide a guide to the use of Cybyr-AI, its scope, output and what you can expect to expect from using the software. |
Intention
|
AI COMPARISONS - How Cybyr-AI is Unique
This table helps clarify the ten most important differences between our new Proactive, Expert Guided AI, Generative AI and Agentic AI.
| Aspect | Proactive Expert-Guided AI (Cybyr-AI) | Generative AI | Agentic AI |
| 1. Goal | Improve outcomes by guiding the user with expert logic | Respond to prompts with knowledge or creativity | Autonomously complete tasks with minimal input |
| 2. Guidance | Asks users questions, suggests next steps | User must steer and prompt repeatedly | Self-directed, but often unfocused |
| 3. Measurability | Scores and tracks user progress over time | No awareness of time, progress, or performance | Logs steps, but doesn’t assess outcomes |
| 4. Trust & Explainability | Based on vetted expert content | Sometimes great, sometimes misleading | Opaque; difficult to verify why actions were taken |
| 5. Context Awareness | Maintains role, state, and risk profile per user | Remembers context only during one session | Builds memory through chained logic, not user modeling |
| 6. Security | Private, isolated, no external LLMs | Public LLMs with uncertain data use | High risk due to integrations and autonomous behavior |
| 7. Cyber Use Readiness | Built for business security, with structured layers | Good at explaining concepts; not trustworthy alone | Not enterprise-ready for secure domains |
| 8. Alignment with Humans | Designed to support decisions, not replace them | Great assistant, but passive | May act without alignment to values or goals |
| 9. Usefulness to SMBs | Guides those with limited security staff or budget | Useful but overwhelming without support | Requires setup, maintenance, and debugging |
| 10. Outcome Orientation | Moves users toward reduced risk and resilience | Provides information; outcome depends on user | May complete tasks, but success is inconsistent |
Introduction: The Journey to Cybyr-AI:
This is the continuation and expansion of the article published in the summer 2025 edition of ISE magazine (on the right. It begins with the “why” that led to the development of Cybyr-AI.
The story starts with the challenging journey into the unknown that we are all facing. I wrote my first data-driven guidance and measurement application when I founded my software company three decades ago. AI was described as “knowledge-based systems” back in those days!
It became obvious that if I wanted to create an AI-assisted implementation for my cybersecurity software, then I needed to understand the nature of the beast. I rapidly discovered that using GenAI alone was never going to cut it.
Why Is this important - and what inspired Me.
This is the continuation and expansion of the article published in the summer 2025 edition of ISE magazine (on the right. It begins with the “why” that led to the development of Cybyr-AI.
The story starts with the challenging journey into the unknown that we are all facing. I wrote my first data-driven guidance and measurement application when I founded my software company three decades ago. AI was described as “knowledge-based systems” back in those days!
It became obvious that if I wanted to create an AI-assisted implementation for my cybersecurity software, then I needed to understand the nature of the beast. I rapidly discovered that using GenAI alone was never going to cut it.
Therefore, I embarked on a different path that enabled the use of AI while recognizing both its strengths and limitations—and those limitations really don’t become apparent until you use it every day.
My goal was to create a cybersecurity system reflecting my organization’s purpose – Cybyr.com: Every Organization Protected. The system should make recommendations and measure risk reduction over time.
Much more than that, I wanted users from all types of organizations to be appraised of the very latest developments and ask for information GenAI style but not with the dated, risky large language model (LLM) approach and uncertain privacy. More importantly I wanted to bring guidance and measurable actions to life in the way that a human subject matter expert can do – but GenAI cannot.
Understanding the Beast
The reality check on the strengths and limitations of both GenAI and humans that inspired me to take my own path.
Strengths
| GenAI | Humans |
|
|
Limitations
| GenAI | Humans |
|
|
Concerns
- A recent study from Arctic Wolf revealed that AI has replaced malware as the biggest cybersecurity concern. I suspect the fear of the unknown and the opaqueness of LLM privacy are the reasons. Hopefully, this work removes some of these unknowns.
- When an answer is incorrect, GenAI covers up. For example, my wife, Michelle, was working on a project. After two hours of GenAI not completing a task, she asked why. It said, “I’m designed to sound helpful even when I hit hard limits and that creates a gap between what I say I can deliver and what I can actually deliver.”
- Consumption of vast amounts of power and ecological impact with optimism of a solution.
Teaching AI to Communicate Effectively
Certainly, we must adapt. The human will always be the thinker and the controller, and the AI is the accelerator. Understanding the above comparison. Referring to Gen AI as a partner, companion, helper, useful idiot, or expensive parrot gives it human attributes implies human qualities it cannot have. We should avoid that.
What helps is to force context and questioning, limit onformation overwhel, constantly remind it of what you need bause even if it remembers dialogs it cannot ave its own way of communicating. heres some examples.
- “If I need to acomplish Task X which actions must I consider?”
- Conversely, “If I want to acomplish Task Y what questions do you have for me?”
Summary: a Position to Build Something of Great Value
Gen AI is remarkable software programmed to engage the user and yes it often infuriates as a trial-and error machine! Perhaps experience shows us that we are still at the prototype phase. Generative AI does make what we do more valuable, productive and enables our personal creativity. Five years from now many of the issues including the power and ecological issues will be behind us and the very infuriating trial and error based advice on sketchy and outdated information will have been overcome.
It’s the realization that the strengths of both humans and AI can be combined to create something of great value.
Why This All Matters
Cybersecurity is no longer just an IT issue—it’s a business imperative. However, most organizations don’t have the resources to sift through every standard framework or emerging threat.
That’s where this system makes a difference. It distills expert guidance into actionable steps tailored to the user’s context and keeps evolving with new data. The good news is this approach can be applied to adjacent areas: resilience, HR, and, in fact, any guidance or white paper topic that moves from what to do to how to do it.
Guide to Using Cybyr-AI Software

Bringing Expert Guided Actions to Strengthen Your Organization
Step-by-Step: “Getting Started”
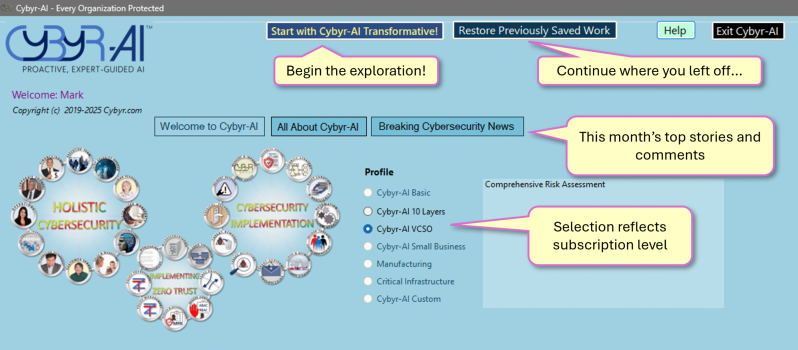

- Conducts a Proactive, investigation of your entire organization – not just IT.
- Takes on human characteristics
- Holistic: examines each department/line of business.
- Makes recommendations and prioritizes your most urgent actions.
- Measures progress to remove vulnerabilities and reduce risk – over time, Transforming your Security Posture.*
- Seamlessly adapts to new threat conditions.
- Especially beneficial for businesses lacking expertise, resources, budget – who are as much under threat as huge organizations.
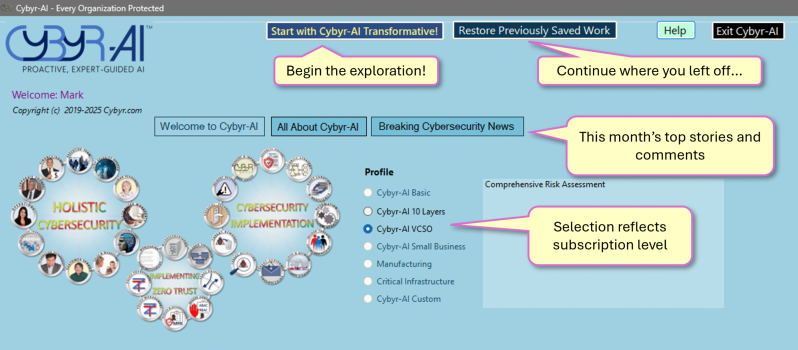
“Begin the interrogation”
Work your way through each outside contractor, internal department and areas of potential vulnerability, areas that require careful management. Upt o16 areas and up to 300 potential answers.
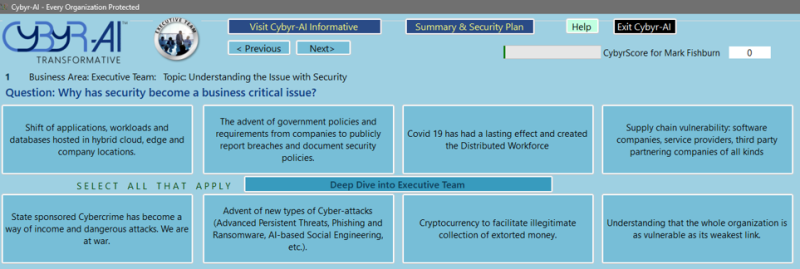
The system builds a picture security posture covering each area of responsibility.
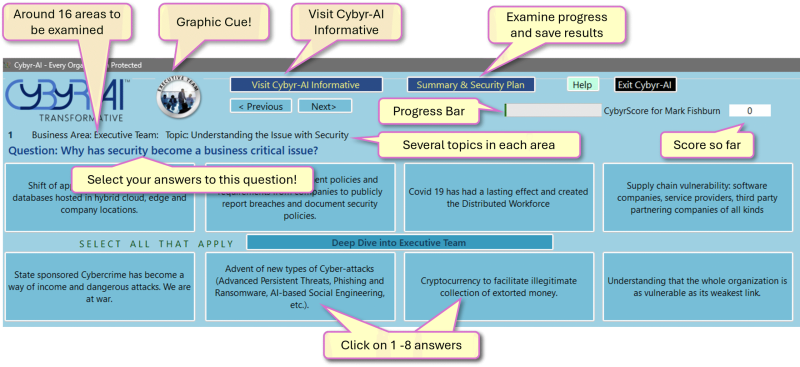
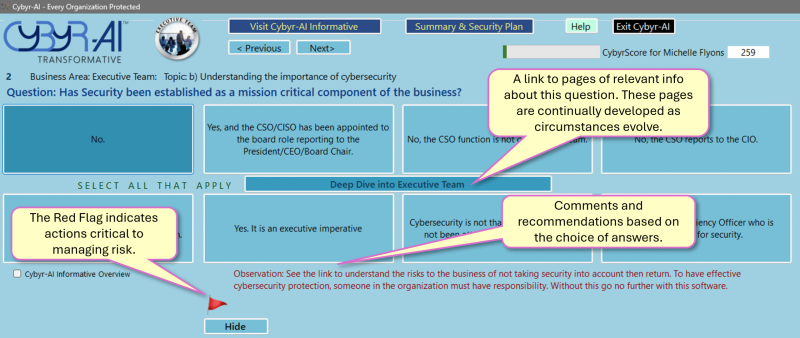
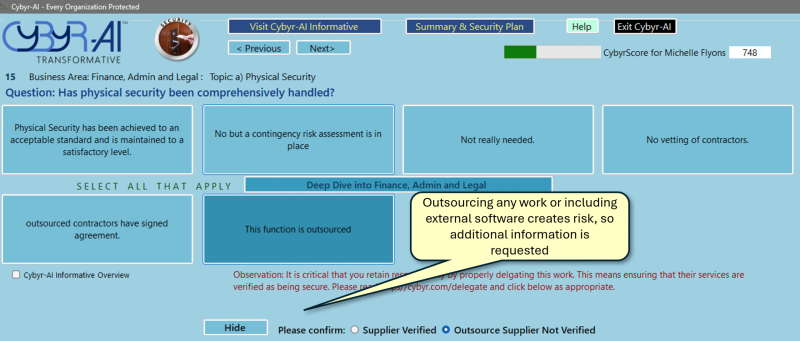
* Security Posture is an organization’s ability to prevent, detect and respond to and recover from security threats and risks.

Automatically Tracking the latest Developments in Cybersecurity
- Delivers the latest Expert Advice from the world of cybersecurity:
- Simple structured approaches to deep dives on every cybersecurity topic.
- Zero Trust frameworks, Resilience, Supply Chain Management & more.
- Up to the moment information on threats, initiatives, guidance, solutions.
- Automatically updates you with the latest news from the Cybyr.com Knowledge Base, the top twelve cybersecurity news sites, blogs, new video series from the experts. No need to seach the Web!
- Instant explanation of 400+ cybersecurity terms, threats and solution types.
- Ask questions of Cybyr-AI and top Gen AI agents, compare results.

Assess Risk Reduction and Strengthening Vulnerabilites Over Time
- Analyzes responses, measures and rates strengths and vulnerabilites by department or line of business and for the whole organization.
- Prioritizes your most urgent actions.
- Measures progress to strengthen each line of business over time.
- Provides new recommendations as progress is made.

Secure By Design
- Uses OpenAI API calls to server-based private secure data not in non-verifiable and public LLMs.
- Implemented with DevSecOps, written in a modern Memory-safe language.
- Does not use open-source or supply chain code.
- User data, results and proprietary information held in clientless environments.
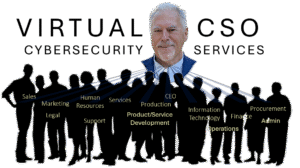
Integrated and Customizable with Cybyr.com’s Virtual CSO Service
Many organizations do not have the time, expertise, budget or the processes to implement all the ideas and possibilities covered in cybersecurity programs even one as integrated as Cybyr-AI. This is where our Virtual Chief Security Officer Service can customize Cybyr-AI and partner with you in overseeing and implementing the recommendations made by Cybyr-AI.
